Documentation Index
Fetch the complete documentation index at: https://slackhive.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
What is MCP?
MCP (Model Context Protocol) is a standard that lets AI agents connect to external tools and data sources. Think of MCP servers as plugins for your agents - they give agents the ability to actually do things beyond just having a conversation. Without MCP, an agent can only talk. With MCP, an agent can:- Query your database and return real results
- Read files from a repository
- Create GitHub issues
- Fetch data from any internal API
- Run custom scripts
You don’t need to build MCP servers from scratch. There are many open-source MCP servers for common tools. SlackHive also supports inline TypeScript MCPs - you can paste code directly into the UI without deploying anything.
How SlackHive manages MCP
SlackHive manages MCP servers at the platform level. You add a server once to the global catalog, then assign it to any number of agents. When an agent starts, SlackHive launches all its assigned MCP servers and keeps them running. There’s no per-message startup overhead - once the agent is live, its tools are always ready. Tool names follow the patternmcp__{serverName}__{toolName}. For example, a server named redshift with a query tool is called as mcp__redshift__query.
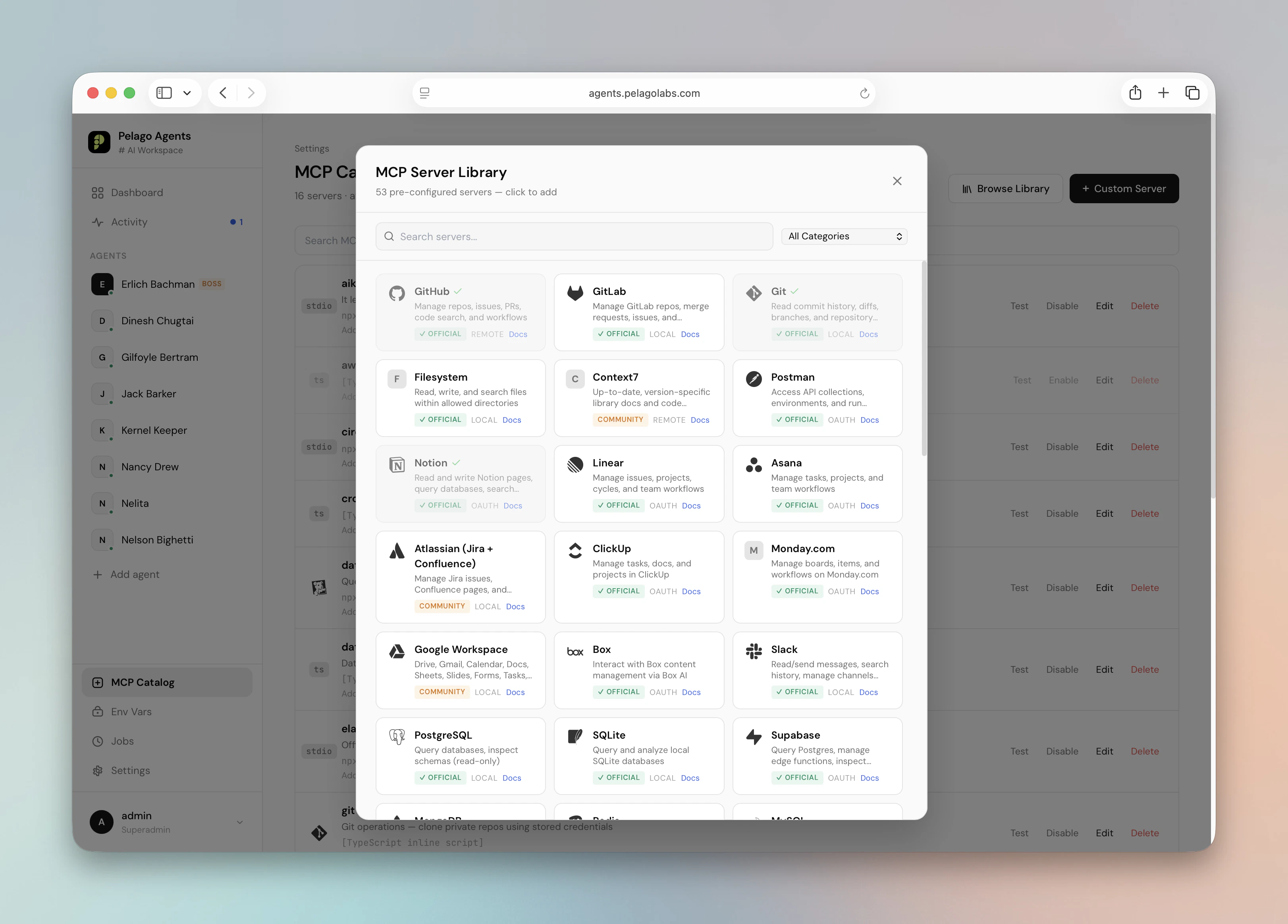
The catalog - Official vs Community
The platform catalog surfaces two badges:| Badge | Meaning |
|---|---|
| Official | Curated template maintained by SlackHive - tested and kept in sync with upstream MCP packages |
| Community | Server you or a teammate added - not vetted |
Adding a server to the catalog
Pick a starting point
Three options:
- Browse Templates - pick from 40+ Official and Community templates
- Import from Claude Code CLI - one-click add any MCP already registered in your local
claudeCLI (shows a CLI badge on the card) - Custom Server - paste a Cursor / Claude Desktop / VS Code config, or fill in fields
Fill in the blanks
In Custom Server the default view is a JSON textarea that accepts the standard
{ "mcpServers": { ... } } shape used by Cursor, Claude Desktop, and VS Code. Use ${env:NAME} for secrets - see Paste JSON from other tools below. Prefer granular fields? Switch to the Form tab.Probe the server
Click Test Connection. SlackHive runs a real MCP handshake -
initialize, tools/list - against the server. You see the list of tools it exposes. If the probe fails, the error is shown inline with the tool stderr.Import from Claude Code CLI
If you’ve already set up MCPs via theclaude CLI (claude mcp add ...), SlackHive can import them one-click.
- In MCP Servers, click Import from Claude Code
- You see the full list from
claude mcp list - Click Import on any server - it’s added to the catalog with a CLI badge
- Adjust the env and config as needed
claude locally.
Transport types
There are four ways to run an MCP server:| Transport | Use case |
|---|---|
stdio | A local process (Node.js script, Python script, binary) - most common |
sse | A remote server accessible via HTTP server-sent events |
http | A remote server accessible via HTTP |
| TypeScript inline | Paste TypeScript source directly - no deployment needed |
Configuration examples
These examples use the standard Cursor / Claude Desktop / VS Code shape - paste them directly into the JSON textarea in Custom Server.Redshift / Data Warehouse
Give your data analyst agent the ability to run real SQL queries:Filesystem Access
Give an agent read access to files in a directory - useful for code review or documentation agents:mcp__filesystem__read_file, mcp__filesystem__list_directory, etc.
Remote API (SSE)
Connect to a remote MCP server over the network:Bearer prefix stays literal; ${env:ANALYTICS_TOKEN} is resolved at spawn time and the runner assembles the final header value.
Paste JSON from other tools
The Custom Server editor opens on a JSON textarea by default. It accepts the same{ "mcpServers": { ... } } shape used by Cursor, Claude Desktop, and VS Code - so any config you already have elsewhere can be pasted verbatim.
Two shapes are accepted:
${env:NAME} substitution. Any value matching ${env:NAME} is mapped to the SlackHive encrypted env store. At spawn time the runner resolves the reference and injects the secret into the subprocess environment - the raw value never lands in the config row. Prefixes are preserved, so "Authorization": "Bearer ${env:GH_TOKEN}" resolves to Bearer <secret>.
Missing env vars. If your JSON references an env var that doesn’t exist in the store yet, a chip appears under the textarea. Click it to set the value inline without leaving the editor.
Editing existing servers. Reopening a saved server re-serializes its config back to the JSON shape. Inline secrets come back as "********" - leave them alone to preserve the stored value, or replace with a real value or ${env:NAME} ref to change it.
Form mode. A Form tab next to JSON exposes the granular fields for users who prefer them. Toggling seeds the other view, so switching mid-edit doesn’t lose work.
Inline TypeScript
The most convenient option for internal tools: paste TypeScript source directly into the UI. SlackHive writes it to disk and runs it - no separate deployment needed. Select TypeScript inline script as the transport type, then paste your implementation:Assigning servers to agents
Once a server is in the catalog, you can assign it to agents:- During agent creation - Step 4 (Tools) of the wizard
- After creation - from the agent’s Tools tab
Who can assign which MCP
The catalog is workspace-wide — every authenticated user sees every MCP — but assignment is gated by ownership:| Role | What they can assign |
|---|---|
| Editor | Only MCPs they created (createdBy = themselves) |
| Admin / Superadmin | Any MCP regardless of owner |
🔒 owned by <user> badge with a disabled checkbox; the API rejects unauthorized assignment with a 403 naming the specific MCP. The intent is that an MCP holding production credentials (a private database PAT, a paid API key) can only be wired into agents by the person who configured it — or an admin who has explicit authority.
To hand off ownership, the current owner deletes their MCP and the new owner re-creates it, or an admin updates the created_by column directly.
Keeping secrets safe
Never paste database credentials, API keys, or passwords directly into MCP configenv fields. Use the encrypted env store instead.
The env store encrypts secrets at rest using AES-256. Values are never returned by the API or shown in the browser - only the key names are visible.
Add your secret to the store
- Go to Settings → Env Vars in the sidebar
- Click Add Variable
- Enter a name (e.g.
REDSHIFT_DATABASE_URL) and the secret value - Click Save - the value is encrypted immediately
"********" in place of any inline secret values you did paste literally - leaving them untouched preserves the stored value.
Testing a server
From Settings → MCP Servers, any user with an editor role or above can click the Test button next to any server — regardless of who created it. SlackHive runs a full MCP handshake:- Launches the server process (or connects to the remote URL)
- Sends
initialize - Sends
tools/list - Displays the discovered tools inline
OAuth MCPs
Some servers (Figma, Linear, remote Anthropic MCPs) require OAuth. SlackHive supports three OAuth flows:- Dynamic client registration - click Connect in the catalog, complete the OAuth dance
- Paste token - for providers that block dynamic registration
- Claude Code CLI import - if the MCP is already authorized in your local
claudeinstall
Next steps
Agent Tools & Permissions
Control exactly which MCP tools each agent can use.
OAuth MCPs
Connect servers that require OAuth authentication.